The Role of PCI DSS Consulting Services in Tokenization & Encryption Strategies
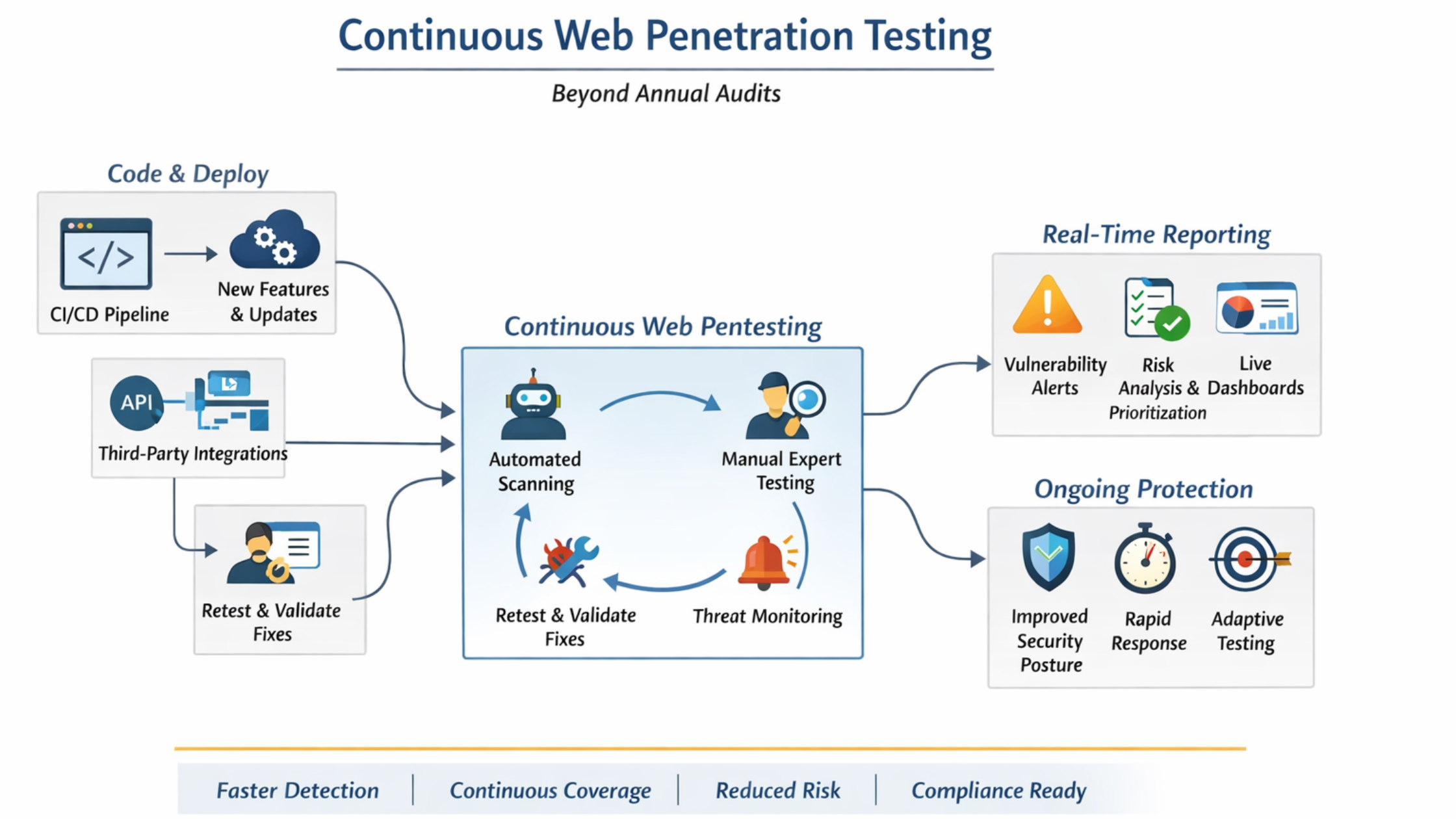
As payment environments become more distributed—spanning cloud platforms, APIs, mobile apps, CI/CD pipelines, and third-party services—protecting cardholder data is no longer just about “encrypting the database.”
Modern PCI DSS compliance depends on how encryption and tokenization are designed, implemented, governed, and validated across the entire payment data lifecycle.
PCI DSS Consulting Services play a critical role in this shift. Their value is not limited to documentation or audits; instead, they help organizations architect cryptographic controls that actually reduce PCI scope, resist modern attack techniques, and align with PCI DSS v4.0’s intent-based requirements.
This blog explores how PCI DSS Consulting Services influence tokenization and encryption strategies at an architectural, operational, and governance level, going beyond textbook definitions into real-world implementation challenges.
Tokenization and Encryption Are No Longer “Security Tools” — They Are Compliance Architecture Decisions
In mature payment environments, encryption and tokenization are foundational design choices, not add-on controls. A poorly designed encryption strategy can still leave organizations exposed to scope creep, key compromise, audit failures, and breach impact.
PCI DSS Consulting Services help organizations make strategic decisions, such as:
- Where encryption is sufficient
- Where tokenization is mandatory
- How to minimize exposure of Primary Account Numbers (PAN)
- How to align cryptography with application workflows and cloud services
Key Architectural Focus Areas Consultants Address
- End-to-end cardholder data flow mapping
- Identification of cryptographic trust boundaries
- Selection of tokenization models (vault-based vs vaultless)
- Alignment with PCI DSS v4.0 Requirements 3 & 4
- Operational feasibility across DevOps and production
The Consultant’s Role in Designing Tokenization Strategies That Actually Reduce PCI Scope
Tokenization is often misunderstood as a simple replacement of PAN with random values. In reality, tokenization strategy defines the PCI boundary of your entire organization.
PCI DSS Consulting Services help design tokenization systems that:
- Eliminate PAN from most systems, not just mask it
- Prevent token re-identification outside approved zones
- Support scalability without increasing compliance overhead
How Consultants Approach Tokenization Design
Rather than asking “Can we tokenize?”, consultants ask:
- Where should PAN exist at all?
- Which systems truly require access to real card data?
- How can tokens support business processes without exposing risk?
Strategic Tokenization Decisions Guided by PCI DSS Consultants
- Choosing between vault-based tokenization and format-preserving tokenization
- Determining whether tokens should be single-use, session-based, or persistent
- Designing segregated token vault architectures
- Defining token lifecycle management (creation, usage, revocation, rotation)
- Ensuring tokens are irreversible without privileged access
Encryption Strategy Under PCI DSS v4.0: Beyond “AES-256 Everywhere”
PCI DSS v4.0 moves away from checkbox compliance and focuses on cryptographic intent, effectiveness, and operational maturity. Encryption must now be demonstrably strong, properly managed, and resistant to both external and internal threats.
PCI DSS Consulting Services help organizations design encryption strategies that withstand:
- Cloud misconfigurations
- Insider threats
- Compromised workloads
- API abuse
- Key exposure incidents
Consultant-Led Encryption Strategy Components
Consultants assess encryption across:
- Data at rest
- Data in transit
- Data in use (where applicable)
- Key management infrastructure
Core Encryption Decisions Consultants Validate
- Algorithm selection based on data sensitivity and use case
- Cryptographic module compliance (FIPS 140-2/3 where applicable)
- Key size, rotation frequency, and lifecycle controls
- Hardware Security Module (HSM) vs cloud-native KMS
- Separation of duties between key custodians and system administrators
Why Key Management Is the Real Compliance Battlefield
Encryption without strong key management does not reduce PCI risk.
PCI DSS Consulting Services place heavy emphasis on cryptographic key governance, which is frequently where organizations fail audits.
Consultants help organizations design key management systems that ensure:
- Keys are never stored with encrypted data
- Key access is strictly role-based and logged
- Key compromise does not expose historical data
- Cryptographic operations are auditable and controlled
Key Management Areas Consultants Focus On
- Centralized vs decentralized key storage
- Bring Your Own Key (BYOK) and Hold Your Own Key (HYOK) models
- Key rotation automation and enforcement
- Secure key backup and destruction procedures
- Incident response processes for suspected key compromise
Tokenization + Encryption: Designing Layered Protection, Not Redundant Controls
A common mistake is treating tokenization and encryption as interchangeable. In reality, PCI DSS Consulting Services design layered strategies, where each control serves a distinct purpose.
How Consultants Combine Tokenization and Encryption
- Tokenization to eliminate PAN exposure
- Encryption to protect remaining sensitive data
- Strong key management to enforce trust boundaries
- Access control and monitoring to detect misuse
Practical Layering Examples
- Encrypt PAN at ingestion, tokenize immediately after authorization
- Store encrypted PAN only in isolated, high-trust systems
- Use tokens across applications, logs, analytics, and support tools
- Encrypt token vaults separately with dedicated key hierarchies
Aligning Tokenization & Encryption with PCI DSS v4.0 Intent-Based Controls
PCI DSS v4.0 emphasizes security outcomes, not just technical implementation. Consulting Services help organizations demonstrate that cryptographic controls:
- Reduce attack surface
- Limit blast radius of breaches
- Are actively managed and monitored
PCI DSS v4.0 Areas Where Consultants Add Value
- Mapping encryption controls to risk analysis outcomes
- Justifying compensating controls with evidence
- Aligning cryptography with customized implementation approaches
- Supporting QSA reviews with technical documentation and logs
Tokenization and Encryption in Cloud & API-Driven Payment Architectures
Modern payment systems rely heavily on APIs, microservices, containers, and serverless functions. PCI DSS Consulting Services help adapt cryptographic strategies to these environments without breaking scalability or performance.
Cloud-Specific Challenges Consultants Address
- Ephemeral workloads and short-lived secrets
- Multi-tenant infrastructure risks
- API-level data exposure
- Shared responsibility misunderstandings
Consultant-Guided Cloud Encryption Strategies
- Envelope encryption using cloud KMS
- Service-to-service encryption using mTLS
- Token propagation across microservices
- Secure secret injection into CI/CD pipelines
Operationalizing Tokenization & Encryption Across DevOps and Security Teams
Encryption and tokenization fail when they remain security-only initiatives. PCI DSS Consulting Services help embed these controls into daily operations.
Operational Areas Consultants Strengthen
- Secure coding standards for cryptographic usage
- CI/CD pipeline checks for encryption enforcement
- Monitoring and alerting for cryptographic failures
- Change management for key and token systems
- Developer training focused on misuse prevention
Common Failures PCI DSS Consultants See — and How They Fix Them
Even mature organizations struggle with cryptographic implementation. Consulting Services bring experience from multiple environments to identify patterns of failure.
Frequent Tokenization & Encryption Gaps
- Tokens that can be reversed without strong authorization
- Encryption keys accessible to application administrators
- Static keys never rotated
- Logs containing sensitive data before tokenization
- Weak separation between production and non-production cryptographic controls
How Consultants Remediate These Issues
- Redesigning trust boundaries
- Introducing cryptographic role separation
- Automating rotation and monitoring
- Refactoring data flows to reduce exposure
- Aligning security architecture with audit evidence requirements
Measuring Success: What “Good” Looks Like in PCI DSS Cryptographic Strategy
PCI DSS Consulting Services define success not by tool deployment, but by measurable risk reduction.
Indicators of a Mature Strategy
- Minimal systems in PCI scope
- Token usage across all non-essential workflows
- Strong key governance with audit-ready evidence
- Automated enforcement of cryptographic policies
- Reduced remediation findings year-over-year
Conclusion: PCI DSS Consulting Services as Cryptographic Architects, Not Auditors
In 2026 and beyond, PCI DSS compliance will increasingly depend on how well tokenization and encryption are architected, not just whether they exist.
PCI DSS Consulting Services act as:
- Cryptographic strategists
- Compliance architects
- Risk reduction partners
By designing tokenization and encryption strategies that align with business workflows, cloud platforms, and PCI DSS v4.0 intent, consultants help organizations move from reactive compliance to proactive payment security.